Work from Home (WFW) has been and probably will be the new normal for the better part of 2020; especially for most corporate staff.
This is all effort help curb the spread of one of the most infectious and deadly virus; the COVID 19 virus. The internet forms an integral part of the work from home initiative with business operations now being run through the internet.
The vast internet traffic and crashing of the economies have formed breeding grounds for cybercriminals, hackers looking to extract personal information from your digital footprints for resale to third parties or ask you for a ransom as they withhold your information.
It is therefore paramount that you are informed of the very basics of cybersecurity to help you avoid such unfortunate incidences. This piece will provide you with extensive tips on how to stay safe online during this quarantine.
We will also have a glance at the various threats to your privacy, types of threats as well as how to make the use of the internet safe and secure.
Threats to Your Privacy and Personal Data
Hackers, government surveillance agencies, digital marketers, and tech companies are just some of the big threats to your internet privacy and personal data. They will acquire your personal data for their own financial gains.
Organized cybercriminals will code programs to monitor, corrupt, control and intercept your online activities through your devices. They will then siphon your information to servers/ devices and from here they can access and sell it.
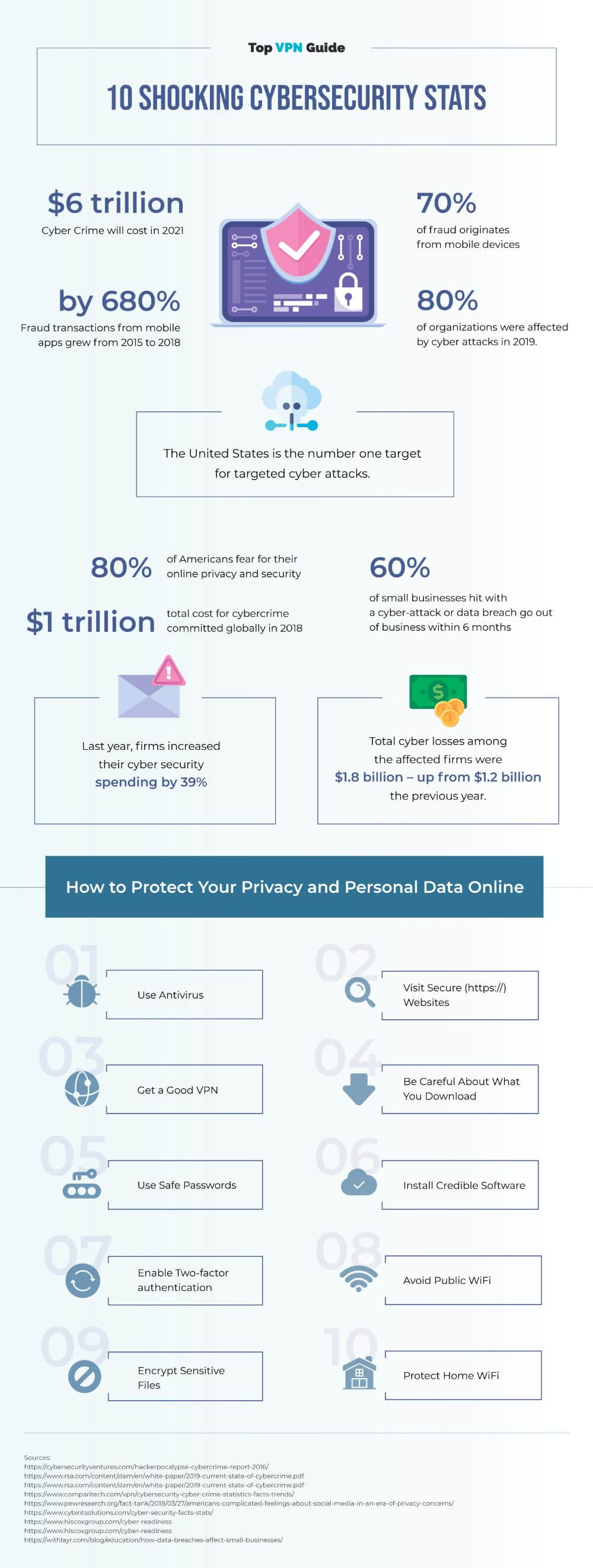
For instance, according to research conducted by McAfee’s Economic Impact of Cyber Crime, it was estimated that close to 780,000 records were lost to hackers every single day. The economic damage of Cybercrime is estimated to reach USD 6 trillion by 2021.
Another survey by the University of Maryland showed that there is a hacker attack every 39 seconds.
81% of organizations were also affected by cyber attacks in 2019.
This goes to show how much you need to protect you data and that of your company as you work from during this unprecedented crisis. Below is a list of types of threats that could expose you to cyber criminals.
Types of Threats

Malware
A malware is basically any malicious software secretly meant to access you computer system. They are designed to tamper with the normal functioning of your computer system.
For instance, they can format your hard drive leading to loss of personal data, alter or delete files, extract/ steal files, take control of your application or even send emails on your behalf.
Virus
It is common name used by media and end users to refer to every other malware. However, viruses are programs designed to attach themselves to computer files and programs.
They originate from shared external storage devices, email attachments and copied server files. Normally, the virus will attach itself to software and replicate once the program is executed and you will end up losing you disk space as well personal data.
In fact, viruses are rare to find; they account for around 10% of malwares and equally hard to get rid of; even with some of the best antivirus software. They most likely quarantine the infected files to cub further replication.
Trojan
Trojans are some of the most common malicious software. Usually you will find them in sent emails, or pop-up windows on websites during your online sessions.
They will masquerade as legit software but will contain malicious instruction that will temper with you computer system. A Trojan horse will only affect you when victim executes it.
Hacker will use Trojan gain a backdoor and access personal data. A perfect example of serious Trojan attack was Trojan Zeus that compromised over 74,000 accounts on websites belonging to NASA, Amazon and Bank of America among others.
Worms
Well, worm have been around since the 1990s; much longer than the viruses. They came into fashion after people and organization began using E-mails. Typically, worm will reach your network and computer through sent email.
In the event that you open email, it replicates itself affecting the entire network system and computer system. One of the famous worm attacks was the love letter worm that originated from the Philippines in 2000.
In its aftermath, the worm left over 50 millions infection and economic losses amounting to USD 6 billion in just 10 days. Computers with expired operating systems and software are most vulnerable to worm attacks.
Spyware
Just like the name suggest these malwares are meant to screen and extract information from your computer and the send it back to the hacker; they are generally programmed to spy on you interaction with the internet.
Spywares will track you keystrokes, delete files, alter you auto signature or even wipe out your hard disk and thereby leading to loss of personal data. They will in most instances appear to you as ads and will replicate ones you click or download them.
Phishing
It is one of the most used methods used by hacker to extract personal data from internet users. In most cases, phishing happen through emails and text messages.
For instances, hacker will send an almost authentic email from big brands companies like Amazon requesting you either buy with them or provide personal details for verification.
It will only appear to you that you have been scammed your money and personal data after you executed their directives.
Ransomware
Here is one of the most common tool used by organized hackers. Such hackers will target companies, government agencies, public figures and you are not also spared such attacks.
According to Emsisoft survey, it was estimated that the US lost close to USD 7.5 billion to Ransomware in 2019. Another report by SonicWall established that there were over 150 million Ransomware attacks in the first 9 months of 2019.
A Ransomware will most likely attack you computer system through phishing, and ads pop ups on websites. The ransomware will then block you from using you computer system with a pop up image demanding for money to be wired to regain access.
How to Protect Your Personal Data Online

Here are few vital tips that will help you protect your privacy online as well as your personal data online criminal and snoopers.
Steps to Protect Your Personal Data:
Secure your home network
Before using you home WIFI network always ensure that you router is up-to-date with the latest firmware. This will help you seal vulnerabilities that may seem as weak points for hackers and online eavesdroppers.
You can also attempt to filter MAC addresses. This way it will be impossible for foreign devices to connect to you home network.
Additionally, you can also opt to create a guest network for you visitors, friends and family. This will leave you work network independent from any other devices that maybe used to accesses any personal / work data.
Encrypt sensitive files
Encrypting personal and work file should be a good remedy to cub data leakages through the internet. It makes sure that in the off chance that the data is intercepted it unreadable by a third party. Software such as Nordlocker ensures safe end-to-end encryption of files.
Use strong password
Using a strong password is key in making sure that your online personal data is safe. It is crucial you avoid writing down you pass codes on every piece of paper in your room. This dims you vulnerable to hacking and identity theft.
Avoid using the names of family, pets and dates of birth as you password; they are quite predictable.
Besides, do not use the one password for all your accounts.
A strong password should at least involve 12 different characters; a mixture of numbers, symbols lower case and uppercase letters.
Use password keeper to keep all passwords safe and secure – you’ll only need to remember one code to enter the app.
Keep family and friends off work devices
Working from home can be sometimes risky especially if you have young kids and friends at your place. It is essential that there are no third parties using you work devices.
With a third party there is always a chance that something will go wrong especially if they do not understand work protocols and online safety measures. Any kind human error could lead to lose of personal data through malware or hacker attacks.
Find out why you need a business VPN in this article!
How to Make the Use of Internet Safe and Secure

Use a VPN
It is one of the most used and effective in using the internet safely. Virtual Private Network provides you with an opportunity to create a secure private network over the internet of which two or more computers can interact remotely.
The interaction is encrypted by the VPN servers in such a way that they cannot be read by anyone who attempts to intercept the data. The information can only be read when it arrives at its destination and therefore cutting off hackers and internet snoopers. It also provides you with a new IP address which protects you from being targeted by hackers.
Top VPN providers at this moment are NordVPN, Private Internet Access and ExpressVPN.
Practice safe browsing
The internet is full of luring content including ads inviting you to some goodies. Well, most of nice stuff popping up on the internet is just fakes. Most hackers will use such enticing content to lure your to clicking their ads and then what follows is a meltdown of malwares into you system.
Train yourself to be choosy and care when browsing on the internet. A malware attack will most likely lead to loss of online privacy and personal data as well.
Be careful what you download
With the internet being the main source of information and software it important that you are on high alert on what you choose to consume and download from the internet. It is essential that you only download items from trusted sources.
Hackers will trick you into loading software with malicious instruction to steal essential data from your computer system. Such software could range from cool game to utility applications among others. Visit legit websites to download your software.
Make purchases on secure site
With so many businesses now going online, hackers have found new way to extract financial data from customers. They are looking to get hold of your credit card details among other online payment details. It is crucial that you only supply such information to trusted and secure online shopping website. To identify such websites look for a padlock icon next to the address bar.
Download and install an Antivirus program
Internet security is quite complex especially when it come to identifying legit and non-legit items. That is why you will need an antivirus program with an internet security feature. This will help add an extra layer of firewall to when browsing the internet. Equally, always make sure that you only have antivirus installed in your computer.
How to Protect Your Computer from Malware

Below is a list of workable tips that will help you protect your computer for malware infection that could lead to hacks and data loss.
Update your software regularly
Most software developer will provide regular updates to their software. It is vital that you regularly update the software to fix bugs that may end up being loop holes for hackers to attack your system.
Avoid clicking links in emails
According to Microsoft survey, 44% of windows viruses are as result of action by the user. Remember, clicking on links on emails lender you computer vulnerable to phishing, and attacks by worm among other malwares.
Be choosy on your downloads
Hackers will use downloads such as games to infect your device with malwares. It is therefore important that you counter check you source before downloading any item from the internet. It is highly recommended that you only download items from trusted sources.
Install an antivirus software
The internet provides us with a whole range of antivirus software. However, most them are crappy and do not work effectively. Always go software from accredited developers such Avast and kaspersky. Equally, do not install more than one antivirus.
Conclusion
The above tips have proved workable if you are looking on how solve you how to stay safe online problem.
They will definitely help use the internet without necessarily having to trade off you privacy for convenience.
However, it important to note that one of the effective ways of using the internet safely is by using a VPN.
With encryption technology and IP address masking VPN provide you with at most internet security as you work from home.
Check our rankings of the best VPN for Windows and top VPNs for Mac Computers.